Handling 550 5.4.1 Relaying denied During Email Verification API Calls
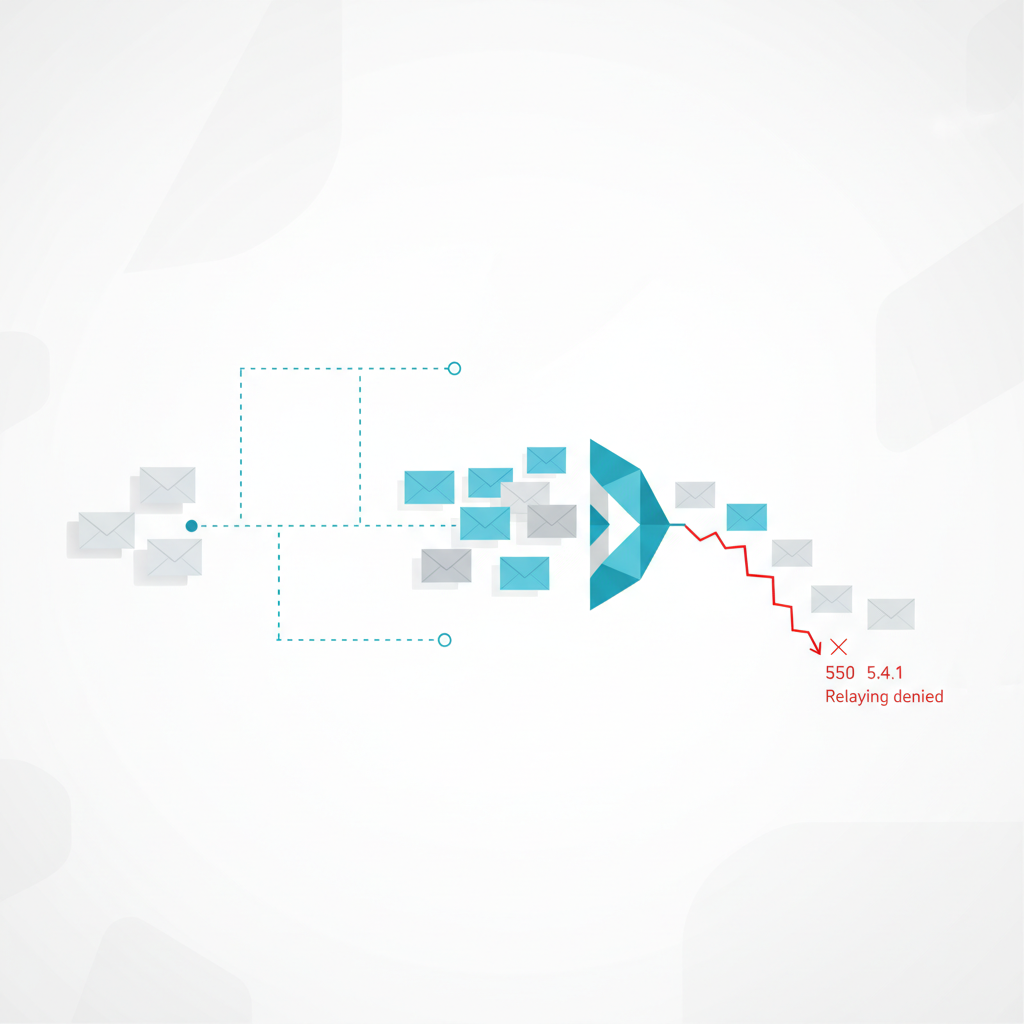
As engineers building robust systems, we're constantly dealing with external services and the myriad error codes they can return. When it comes to email validation, one specific SMTP response you might encounter, especially when delving into the nitty-gritty of real-time probing, is 550 5.4.1 Relaying denied. This isn't your garden-variety "mailbox full" or "user unknown" error; it's a specific gatekeeper message that carries important implications for how you interpret email validity.
This article will break down what 550 5.4.1 Relaying denied means in the context of email verification, why it occurs, and how Verifyr helps you understand and manage this particular signal in your applications.
Understanding 550 5.4.1 Relaying Denied
At its core, 550 5.4.1 Relaying denied is an SMTP (Simple Mail Transfer Protocol) error code. When an email server receives an instruction to deliver mail, it follows a sequence of commands. One crucial step is the RCPT TO: command, where the sending server declares the intended recipient's email address.
A 550 error code indicates a permanent failure. Specifically, 550 5.4.1 Relaying denied means the recipient's mail server refuses to accept mail for that particular recipient from the connecting server (in this case, Verifyr's probing server). The key phrase here is "relaying denied." The server isn't necessarily saying the user doesn't exist; it's saying, "I will not relay mail for this address from you."
Think of it like trying to drop off a package at a private mailroom. If you're not an authorized sender or the package isn't for an internal recipient, they'll deny the drop-off, not because the recipient doesn't exist, but because you're not following their rules for accepting packages.
Why This Error Occurs During Verification
Email verification services like Verifyr perform real-time SMTP probes to determine an email's deliverability. This involves connecting to the recipient's mail server (identified via MX records), initiating an SMTP conversation, and attempting to simulate the early stages of sending an email, up to the RCPT TO: command. We don't actually send an email, but we observe the server's response.
Here's why you might hit a 550 5.4.1 Relaying denied during this process:
-
Anti-Spam and Security Measures: Mail servers are heavily fortified against spam. One fundamental security measure is preventing "open relays." An open relay is a server configured to accept and forward email from any sender to any recipient, regardless of whether the sender is authenticated or the recipient is hosted on that server. Spammers exploit open relays to send vast amounts of unsolicited mail. To combat this, most mail servers are configured to:
- Only accept mail for domains they explicitly host.
- Only accept mail from authenticated users (e.g., your employees logging into their corporate mail server).
- Only accept mail from specific trusted IP ranges.
When Verifyr's probe (which is unauthenticated and coming from an external IP) tries to
RCPT TO:an address, the target server might see this as an attempt to relay mail for a domain it doesn't serve or from an untrusted source, hence the "relaying denied."
-
Recipient Domain Hosting: If the
RCPT TO:address belongs to a domain that the target mail server is not authoritative for, it will deny the relay attempt. For instance, if you connect tosmtp.example.comand try toRCPT TO:<user@anotherdomain.com>,smtp.example.comwill deny it because it's not responsible foranotherdomain.com. Verifyr handles MX record lookups to ensure it connects to the correct server for the recipient's domain, but even then, strict relay policies can trigger this. -
Catch-all Servers with Strict Policies: Some catch-all email servers are configured to be extremely strict with unauthenticated probes. Instead of returning
550 5.1.1 User unknownfor non-existent users (which would reveal their existence), they might return550 5.4.1 Relaying deniedto all unauthenticatedRCPT TOattempts, effectively obscuring whether the user exists or not. This is a security measure to prevent dictionary attacks.
Interpreting 550 5.4.1 in Your Application
When Verifyr encounters 550 5.4.1 Relaying denied, it translates this SMTP response into a structured API response. This isn't a "user unknown" error, nor is it a "mailbox full" error. It's a signal that the target mail server actively refused to process the request for that recipient.
What it doesn't definitively mean: * The email address is invalid. * The user doesn't exist.
What it does mean: * The mail server is configured to deny relaying from unauthenticated sources for that recipient. * Verifyr (and by extension, any unauthenticated sender) cannot definitively determine the existence of the mailbox using a standard SMTP probe. * The email is effectively "undeliverable" via a direct, unauthenticated send.
For your application, this often means treating the email as unverifiable or risky. You cannot confirm its existence, and attempting to send mail to it might result in a bounce if your sending server is also seen as an unauthorized relayer.
Practical Implications and Examples
Let's look at how this manifests and how you might handle it.
Manual SMTP Probe Example
Imagine you're debugging an email address user@strictly-configured-domain.com. You perform a manual SMTP probe using telnet or netcat:
# First, find the MX record for the domain
dig MX strictly-configured-domain.com +short
# Output might be: 10 mail.strictly-configured-domain.com.
# Now, connect to the mail server
telnet mail.strictly-configured-domain.com 25
Once connected, you'd perform the SMTP handshake:
220 mail.strictly-configured-domain.com ESMTP Postfix
HELO verifyr.com
250 mail.strictly-configured-domain.com
MAIL FROM:<probe@verifyr.com>
250 2.1.0 Ok
RCPT TO:<user@strictly-configured-domain.com>
550 5.4.1 <user@strictly-configured-domain.com>: Relaying denied
QUIT
221 2.0.0 Bye
In this scenario, the 550 5.4.1 Relaying denied is explicit. The server refused to accept the RCPT TO command for that address.
Verifyr API Response Example
When you pass an email address like user@strictly-configured-domain.com to Verifyr, and its internal SMTP probe encounters the 550 5.4.1 Relaying denied response, Verifyr will process this and return a structured JSON response.
Here's an illustrative example of what you might receive:
```